On April 19th, 2016, sensitive documents purporting to be from the second largest bank in the Middle East and Africa, Qatar National Bank (QNB), were leaked on a file-sharing site.
In this post, we will show how we leveraged cutting-edge social analytics to unlock insights and reveal new findings on the incident. Additionally, we will show how the customers are coping with the fiasco. Finally, we’ll offer practical brand-saving recommendations.
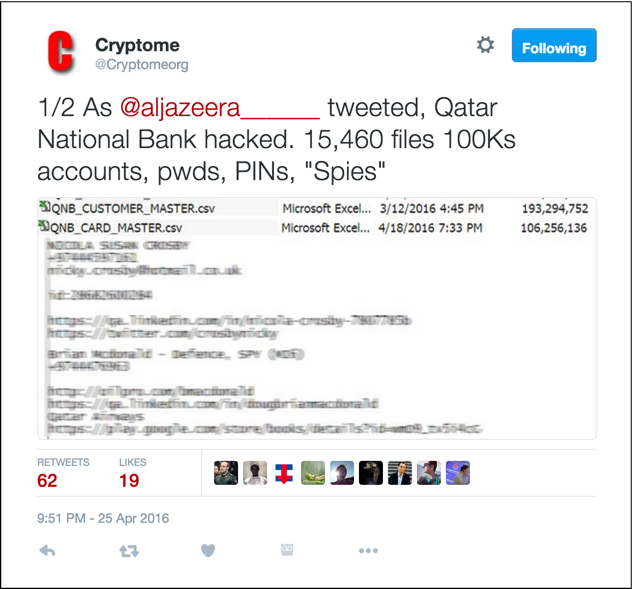
The leak was briefly offered at Global-Files.net, but has since been deleted by the user. The now infamous data breach did not start going viral until the whistleblower clearing house Cryptome re-hosted and released the archive.
Cryptome re-hosts the archive of stolen QNB customers’ data.
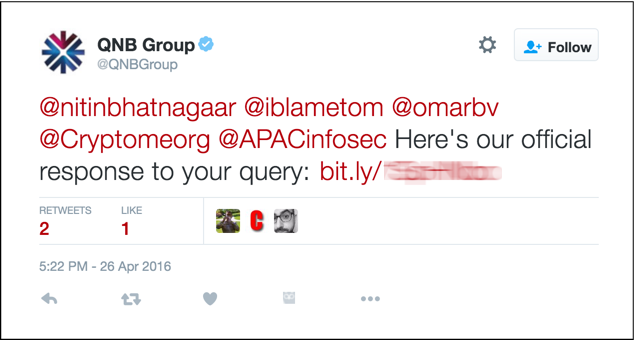
The irony is that QNB Group’s first public response to the incident mentioned Cryptome’s Twitter handle, inadvertently alerting their savvy readers where the sensitive information could be downloaded!
QNB inadvertently tweeting Cryptome’s Twitter handle.
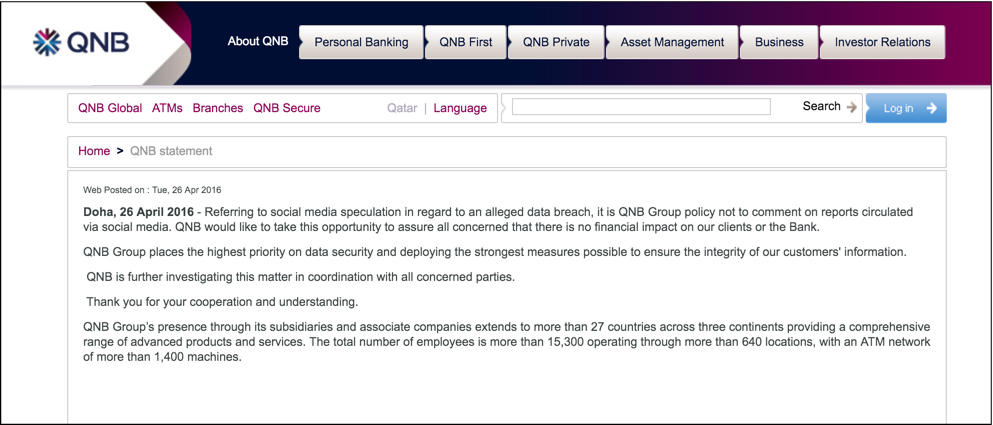
It has been 5 days since QNB issued their public statement on the incident; the bank has not published any further updates or instructions for customers.
Public statement from QNB, and then no further guidance.
The Data Breach Story Breaks
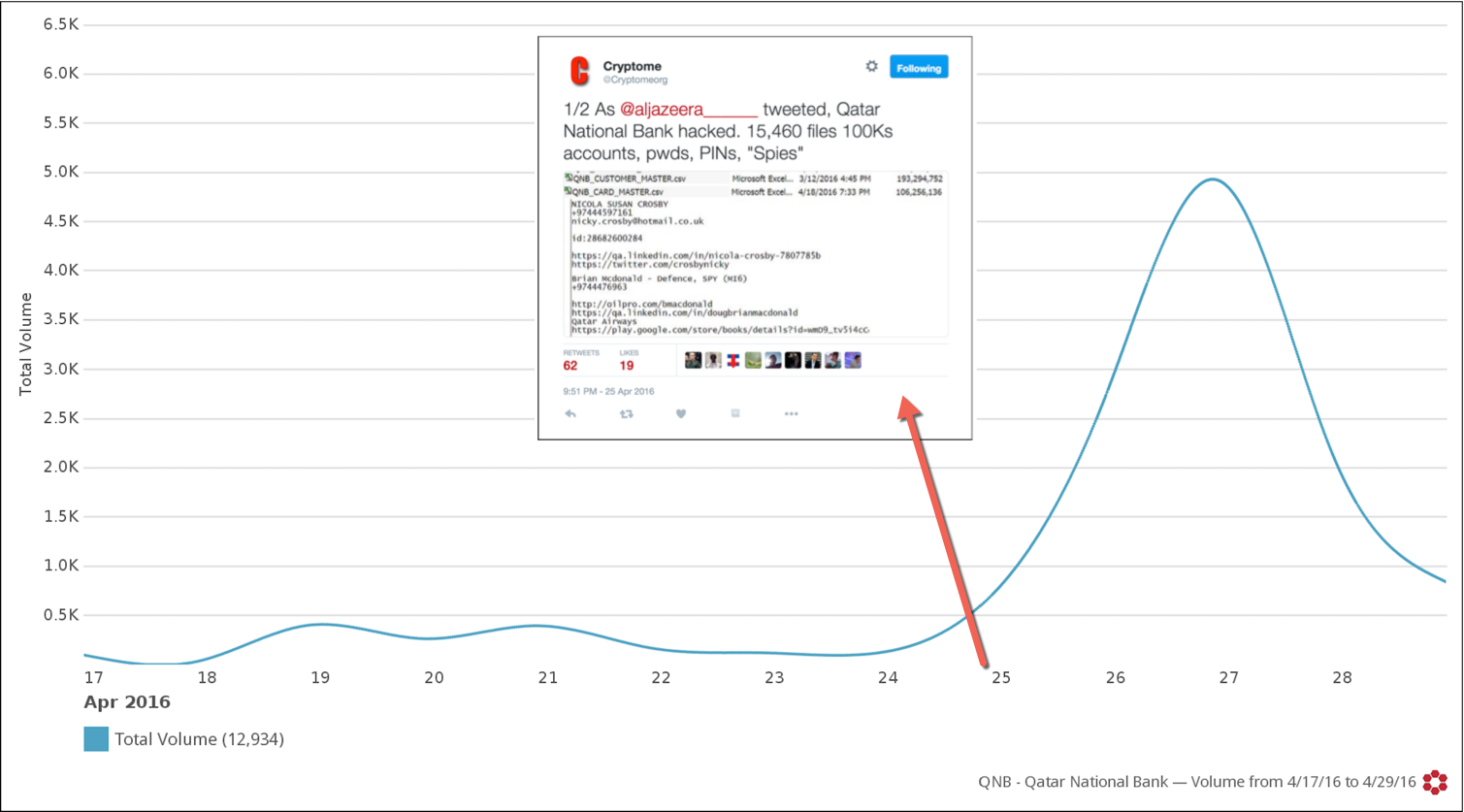
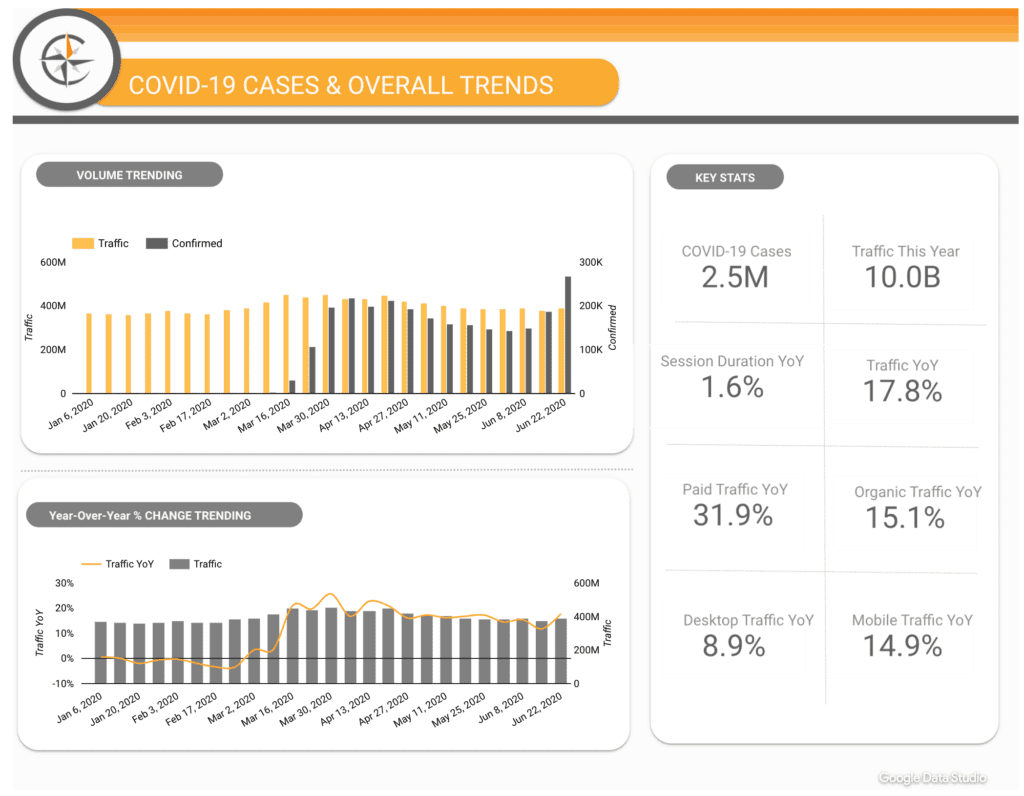
Using Crimson Hexagon’s ForSight™ platform, we analyzed 12,339 Tweets from April 16th through 29th to baseline conversation trends and opinions about the QNB pre and post the news availability to mainstream media. We wanted to find out who got involved, and how the conversations shifted.
Crimson Hexagon ForSight showing the trending for QNB following the breach.
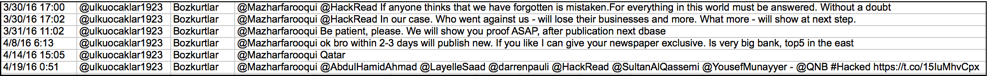
The motivation of the unidentified hacker(s) remains unknown. However, taking advantage of exclusive access to big social data (over 900 billion posts), we were able to analyze posts no longer publicly accessible (authored by suspended accounts). We uncovered the following:
- In early April, a person of interest with a Turkish name of “Boz Kurt“ and a profile picture matching a far-right wing Pan-Turkist organization symbol called “Ülkü Ocaklar?” hinted at a large bank database about to be leaked, later specifically mentioning the country of Qatar. Five days later, the documents were leaked.
Hints of the leak five days before it occurred.
- The same Twitter handle is linked to the mysterious culprit behind the hacking and extorting of Sharjah Bank in November 2015.
- Twitter detected and suspended the account due to spam and cybersquatting.
- Over the next several days, similar messages continued to appear by the authors below:
Tweets from other Twitter handles also suggested an imminent leak.
- Judging by the sequenced posts, author names, time interval between each post, and content, we have a strong reason to believe they all belong to the same person of interest.
The different Twitter handles likely belonged to the same person of interest.
- In desperate attempts to spread the message, the person of interest continued to cycle through accounts and share the message with cyber security experts, news editors, and journalists without much (if any) acknowledgment until Cryptome picked it up.
- Based on the structure of the sentences and choice of words, the person of interest is unlikely to be a native Arabic speaker and perhaps not a native English speaker.
A Deep Dive into Public Perception
Looking broadly at how conversations were trending on Twitter a week prior to the news going viral, there were 1,593 total posts about the QNB, primarily centric to speculations and rumors surrounding QNB acquisition of Kenya’s troubled Chase Bank.
Word cloud for QNB prior to news about the leak.
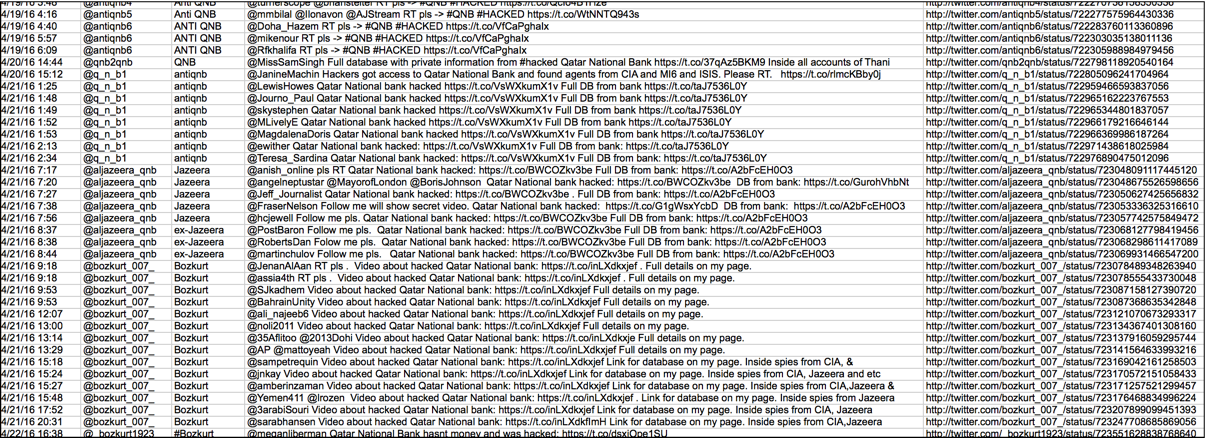
Negative sentiment towards QNB was only 7%.
Just 7% negative sentiment measured prior to news of the breach.
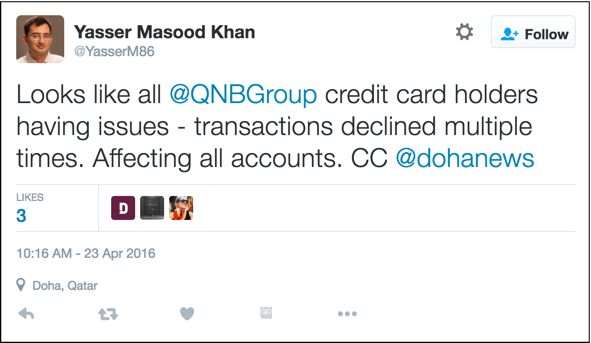
Many of the negative sentiments stemmed from customers’ inability to use their QNB credit cards.
Prior to the leak, negative sentiment about more mundane issues such as inability to use credit cards.
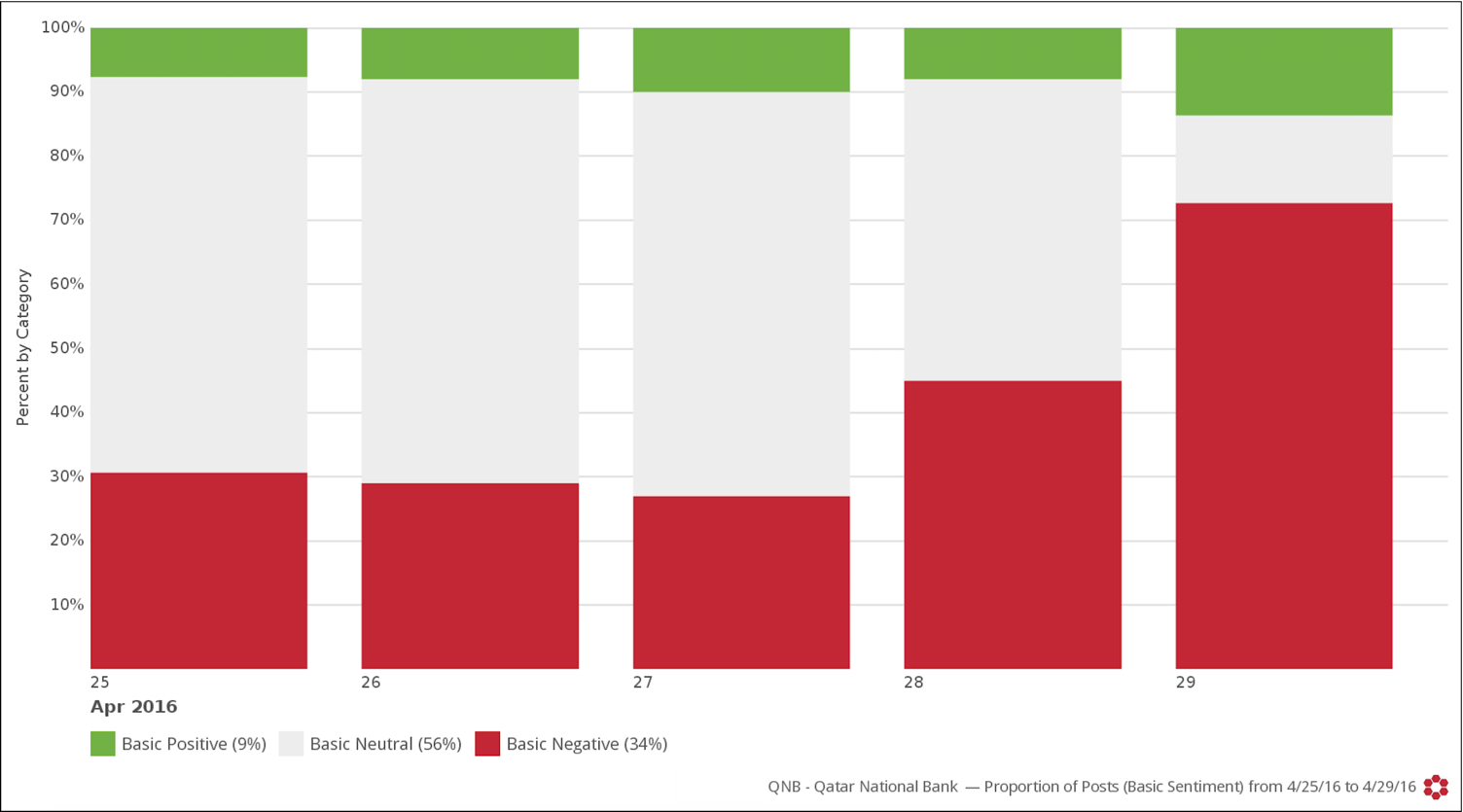
The chatter about QNB quickly spiked after April 24th, as the mainstream media caught up with the data breach story.
Chatter about QNB fanned by mainstream media coverage.
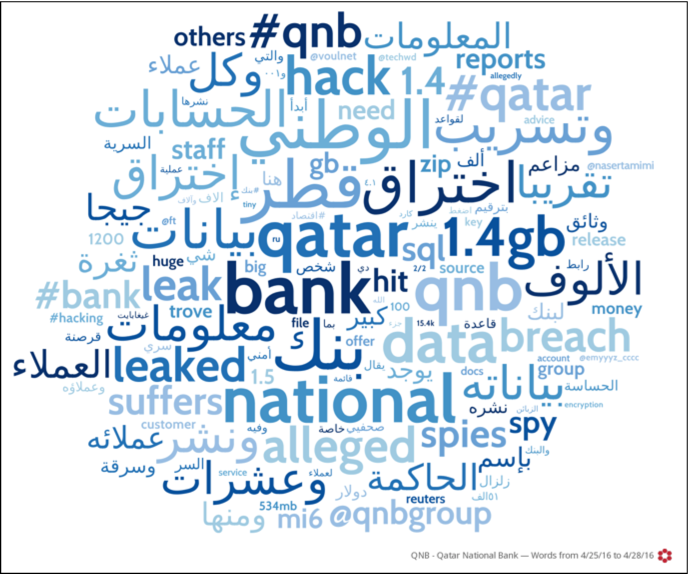
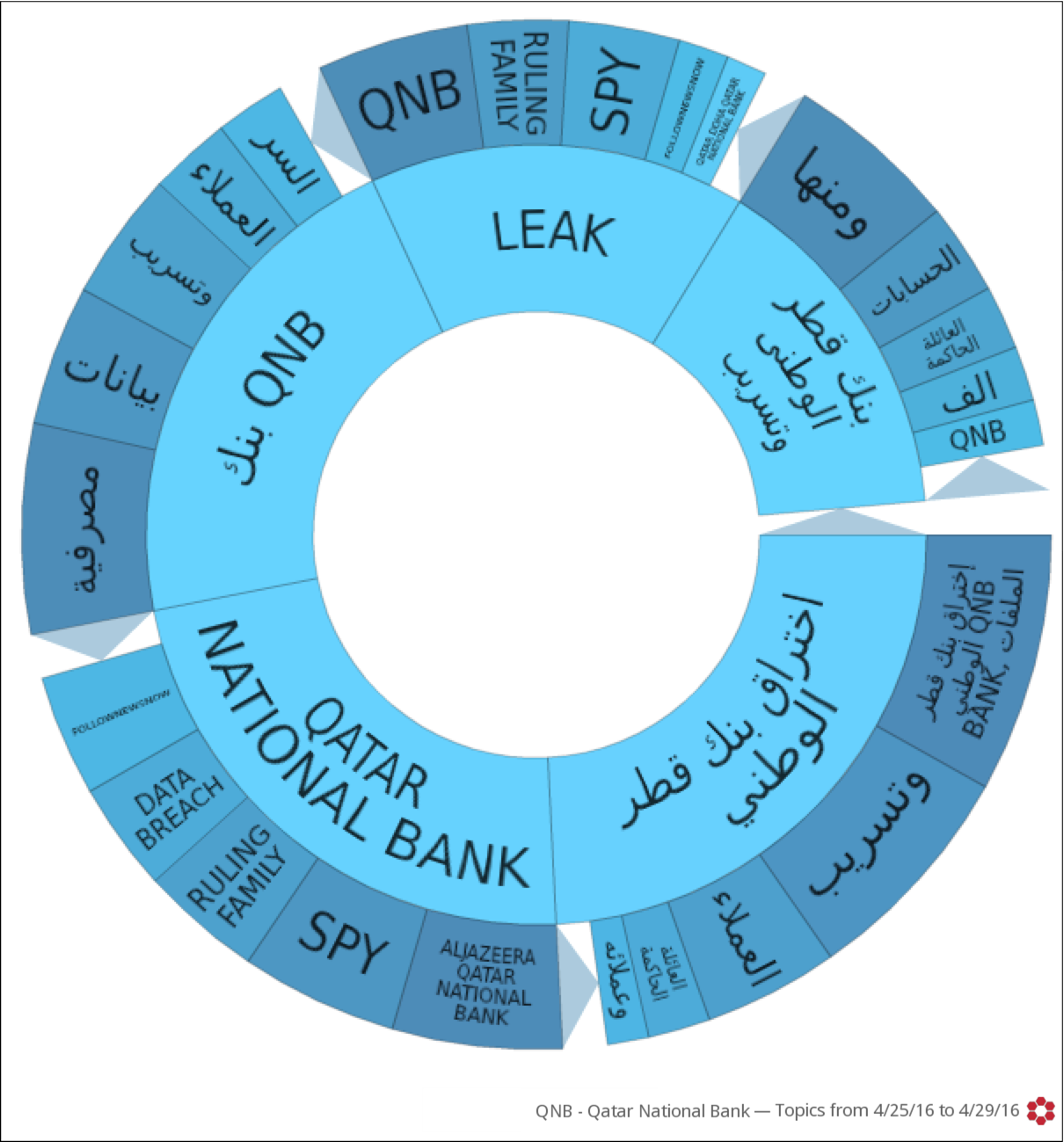
Aggregate customer voice is no longer on mute. Even more revealing, is the nature of the chatter as the conversation heavily focused on the data breach.
A word cloud reveals that the new chatter is focused on the breach.
Topic wheel indicates the same trend.
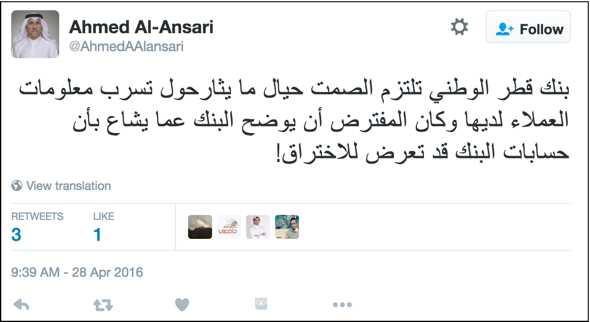
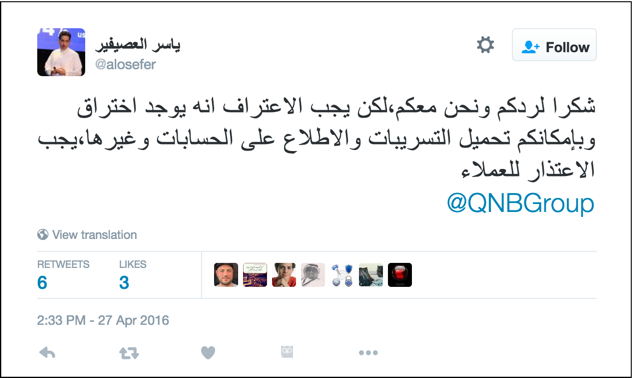
The negative sentiment drivers were mostly QNB’s lack of transparency, response, instructions, and apology.
QNB’s lack of guidance or apology fueled most of the negative sentiments expressed.
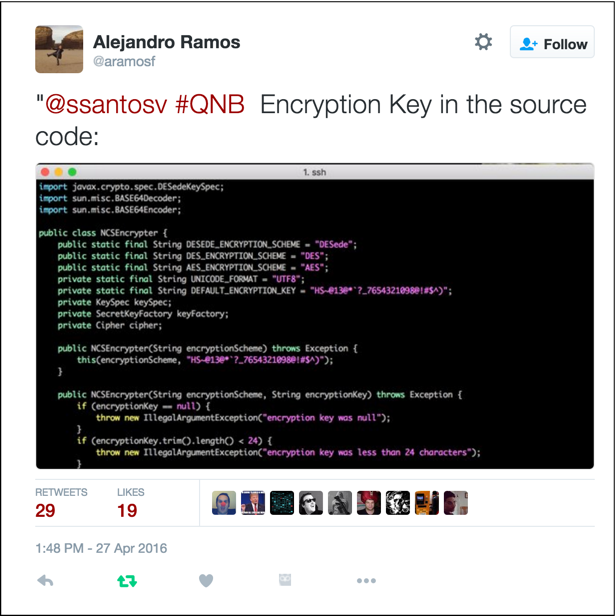
Some security experts have even gone as far as criticizing the security measures in place and pinpointing deadly pitfalls.
Tweet criticizing security lapses.
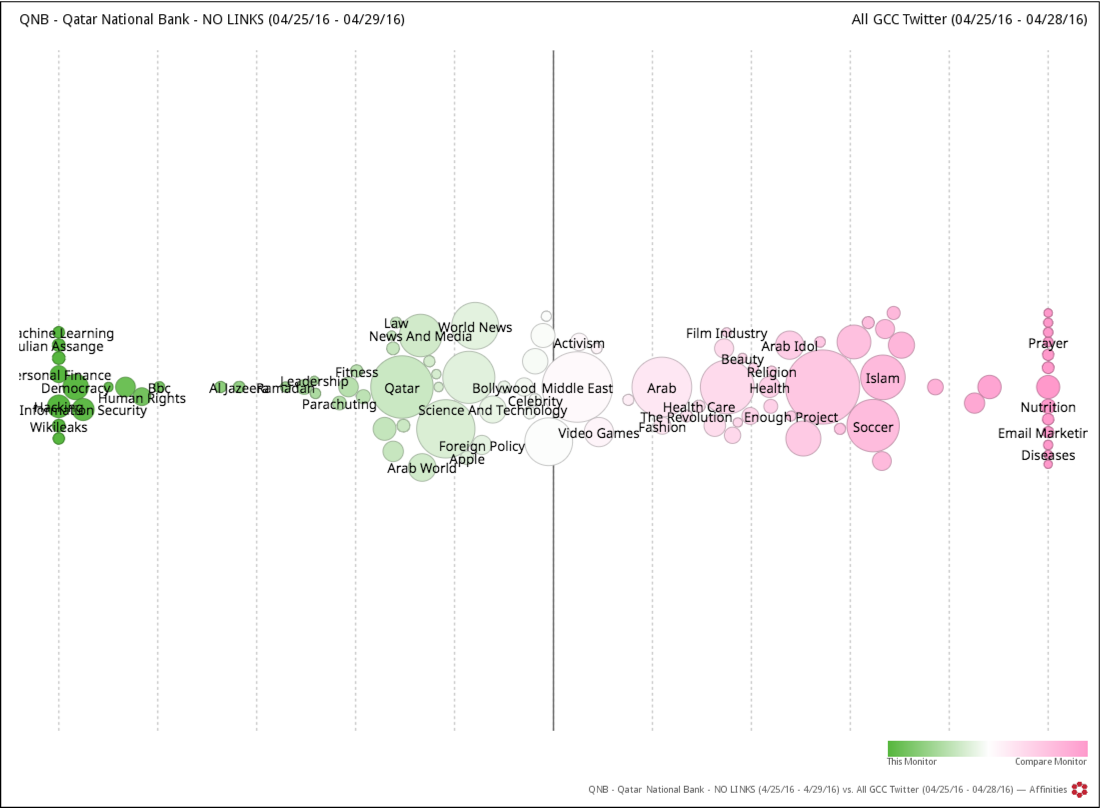
Now stepping away from the “what,” we can focus on who is doing the talking and identify their interests. First, to understand the psychographic profile of the individuals participating in the QNB data breach conversations, we leveraged ForSight’s Affinities tool. This allowed us to dig into the behaviors of the people’s networks and what else they follow and engage in conjunction with a particular topic. Using all of Twitter in the GCC countries as a control group, we can determine the most niche groups.
ForSight’s Affinities tool maps the other subjects of interest for QNB breach tweeters.
Those who participated in the conversations surrounding QNB after the data breach are over 1,000 more likely to be interested in the topics of “hacking”, “machine learning”, “Julian Assange”, “personal finance”, “Wikileaks”, and 40 times more likely to be interested in “information security” and “democracy” than the general broad population swirling in the GCC Twittersphere.
Clearly we are in front of very niche groups of technophiles, news junkies, and those with interest in finance. The psychographic landscape in the GCC region is dominated by interests we see in the right hand of the graph above– soccer, religion, marketing, beauty, Arab idol, revolution, movies, etc.. We therefore wonder why the majority of GCC residents have not yet voiced their opinions on the breach? Perhaps they just haven’t caught up yet with potentially personal implications of the news. These overwhelmingly negative responses may just be the tip of the iceberg for QNB.
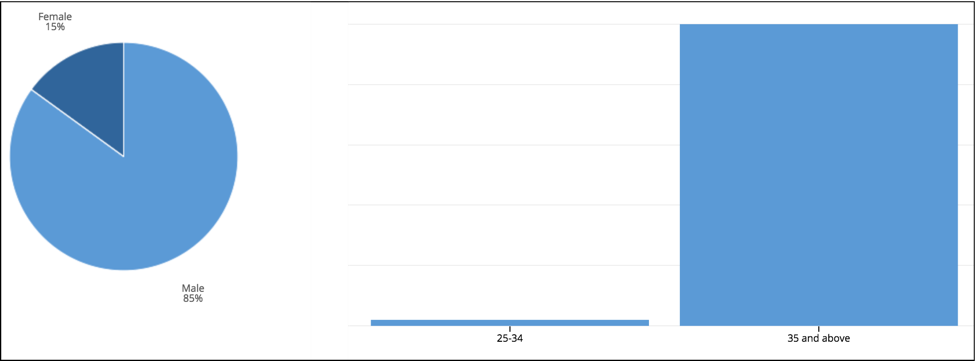
Interestingly over 90% of those who participated in the QNB data breach conversations are 35 years old and above and in which 85% are males.
Age and gender breakdown for participants in the QNB data breach conversation.
Presumably, the issue drew discussion from many adults concerned with their accounts, identifies, data protection and IT security.
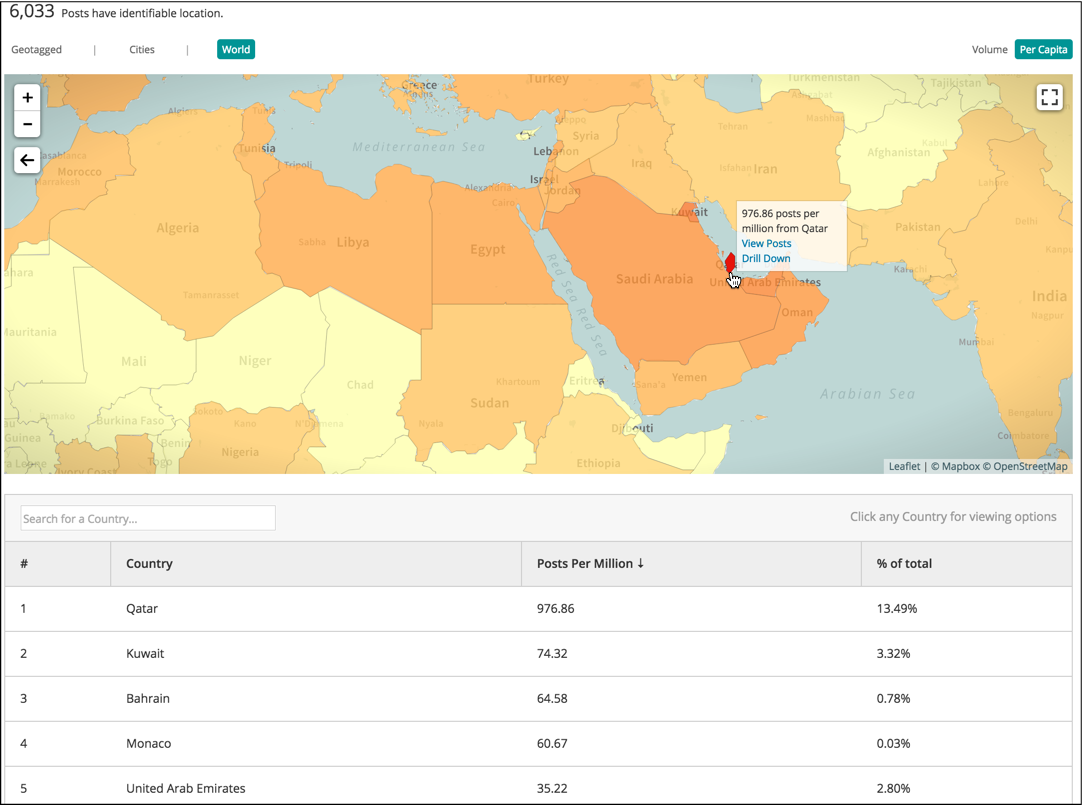
Conversation was also more widespread across the countries and continents with Qatar and other GCC countries taking the lead.
While centered in Qatar, the conversation gained broader geographical reach.
Is There Hope?
No matter how many approval cycles or safeguards are in place, there’s always the possibility that something could go wrong. A brand should not wait until a crisis happens to plan for how to handle it. Mistakes and crises do happen and it is a matter of “when” not “if”. The real question is how well your brand recovers from them. Fortunately, E-Nor consultants can help identify and control fiascos quickly through partnership with the most innovative cutting-edge technologies.
Devise a Plan!
The first step is to define what a crisis looks like for your business. Since social media is increasingly the first place consumers go to express disappointments and frustrations toward a brand, research the missteps of your brand, competitors, or industry to start defining scenarios and start devising a communication and crisis plan. Each scenario may require different reaction and type of messaging. Your community manager also needs to know when to escalate an issue to a brand manager.
You snooze, you lose!
The second step is relentless monitoring. Gone are the days of just monitoring the newspapers. Social media operates at a much rapid pace. No all monitoring solutions are equal. Customers might use the name of your brand, product, campaign, event, or initiative with or without any a “#” or “@” symbols. They may post not just on twitter, but any channel in social, and any news, blogs and reviews site. Does your current monitoring solution covers extensive data sources? Can it help you keep an eagle eye and alert you through email notification when a shift occurs in online conversations towards your business or your competitor business?
Do Not Disappear!
When something goes wrong, people will immediately look at you in social media for acknowledgement. They want to see you are aware of the issue, you’re on it, and you understand you messed up. And when you write to them, write like a human, not a robot. If you can’t respond to each post, at least send a message collectively.
Are You Making a Dent in Resolving Problem?
Crisis can leave a longstanding perception of your brand. Continue to monitor the sentiment. Most important thing to remember is that aggregate data do not tell good stories. Granularity is helpful. Break down the general sentiments into specific drivers of sentiments to tackle. Employ the 80/20 Rule and go after audience segments that harbor more negativity than others.
For additional insights on monitoring the impact of a crisis on your brand, please download the DiGiorno case study from our partner’s site.